近期有需求,讓 Chrome 信任 httpd 中的使用自簽憑證,Google 找到最順利的解決方法:
ssl - Getting Chrome to accept self-signed localhost certificate
步驟如下:
OpenSSL
自建 CA
建立 Private Key (如果不想設密碼就把 -des3 拿掉)
|
|
以剛剛建立的 myCA.key 建立 Root Certficate
|
|
以 Root Certficate 簽署憑證
先設個環境變數儲存 Domain Name 方便之後使用
|
|
建立 Private Key
|
|
建立 CSR (Certficate-Signing Request)
|
|
設定 OpenSSL config (把建立憑證要填的設定寫成檔案比較快)
|
|
產生憑證
|
|
Web Server
把剛剛建好的 $NAME.crt、$NAME.key 裝到你的 Web Server 後重啟即可
<VirtualHost *:80>
ServerName localhost.com
DocumentRoot /var/www/html
CustomLog /var/log/httpd/access.log common
ErrorLog /var/log/httpd/error.log
</VirtualHost>
<VirtualHost *:443>
ServerName localhost.com
DocumentRoot /var/www/html
SSLEngine on
# ========== 安裝自簽憑證 ==========
SSLCertificateFile /root/self-sign/localhost.com.crt
SSLCertificateKeyFile /root/self-sign/localhost.com.key
# ==================================
CustomLog /var/log/httpd/ssl.access.log common
ErrorLog /var/log/httpd/ssl.error.log
Header always set Strict-Transport-Security "max-age=15768000"
</VirtualHost>
SSLProtocol all -SSLv3 -TLSv1 -TLSv1.1
SSLCipherSuite ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY130
5:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-SHA
384:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256
SSLHonorCipherOrder on
SSLCompression off
SSLSessionTickets off
# OCSP Stapling, only in httpd 2.3.3 and later
SSLUseStapling on
SSLStaplingResponderTimeout 5
SSLStaplingReturnResponderErrors off
SSLStaplingCache shmcb:/var/run/ocsp(128000)
重新啟動 httpd
|
|
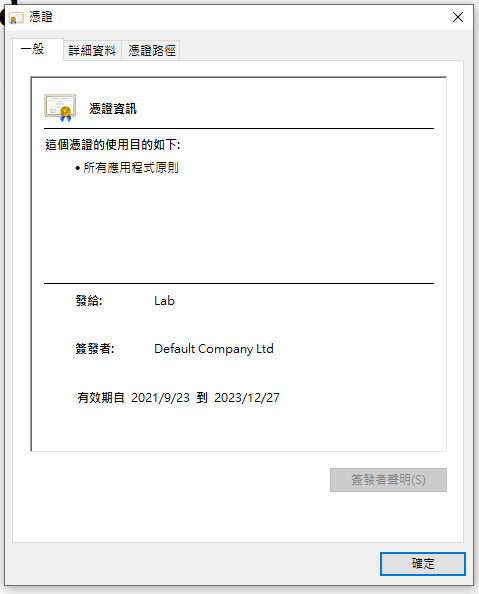
Windows
## 安裝 CA 1. 把 OpenSSL 章節產生的 `myCA.pem` 裝到 Windows 中 2. 重新啟動 Chrome 就完成了